If you built your MVP for speed, the honest answer is usually, “It isn’t.” Upgrading from a startup MVP to an enterprise-grade platform means confronting your data architecture head-on. To pass strict IT audits and achieve SOC2 compliance, refactoring your multi-tenant SaaS database is the most critical engineering investment you can make.
You built a brilliant software product. Users love the interface, your Monthly Recurring Revenue (MRR) is climbing, and you are finally sitting across the table from a Fortune 500 enterprise. They love the tool and are ready to sign a $100k annual contract.
Then, their IT procurement team hands you a 100-point security questionnaire. The deal stalls on a single, critical question: “How exactly is our data isolated from your other clients?”
Here is the technical roadmap for migrating your single-database MVP into a secure, sharded, enterprise-ready architecture.
The Bleeding Neck: The “Shared Everything” Trap
When founders build a Minimum Viable Product, speed to market is the only metric that matters. Developers almost always utilize a “Shared Database, Shared Schema” approach.
In this setup, Client A and Client B store all their user data in the exact same database tables. The only thing separating them is a simple tenant_id column in the code. If a developer writes a buggy API endpoint or forgets to include WHERE tenant_id = X in a query, Client A will suddenly see Client B’s highly sensitive financial data.
For a consumer app, this is a risk. For an enterprise handling proprietary or healthcare data, it is an absolute dealbreaker. They will not sign a contract if a simple coding typo can cause a massive data breach.
The Tourniquet: Architecting a Secure Multi-Tenant SaaS Database
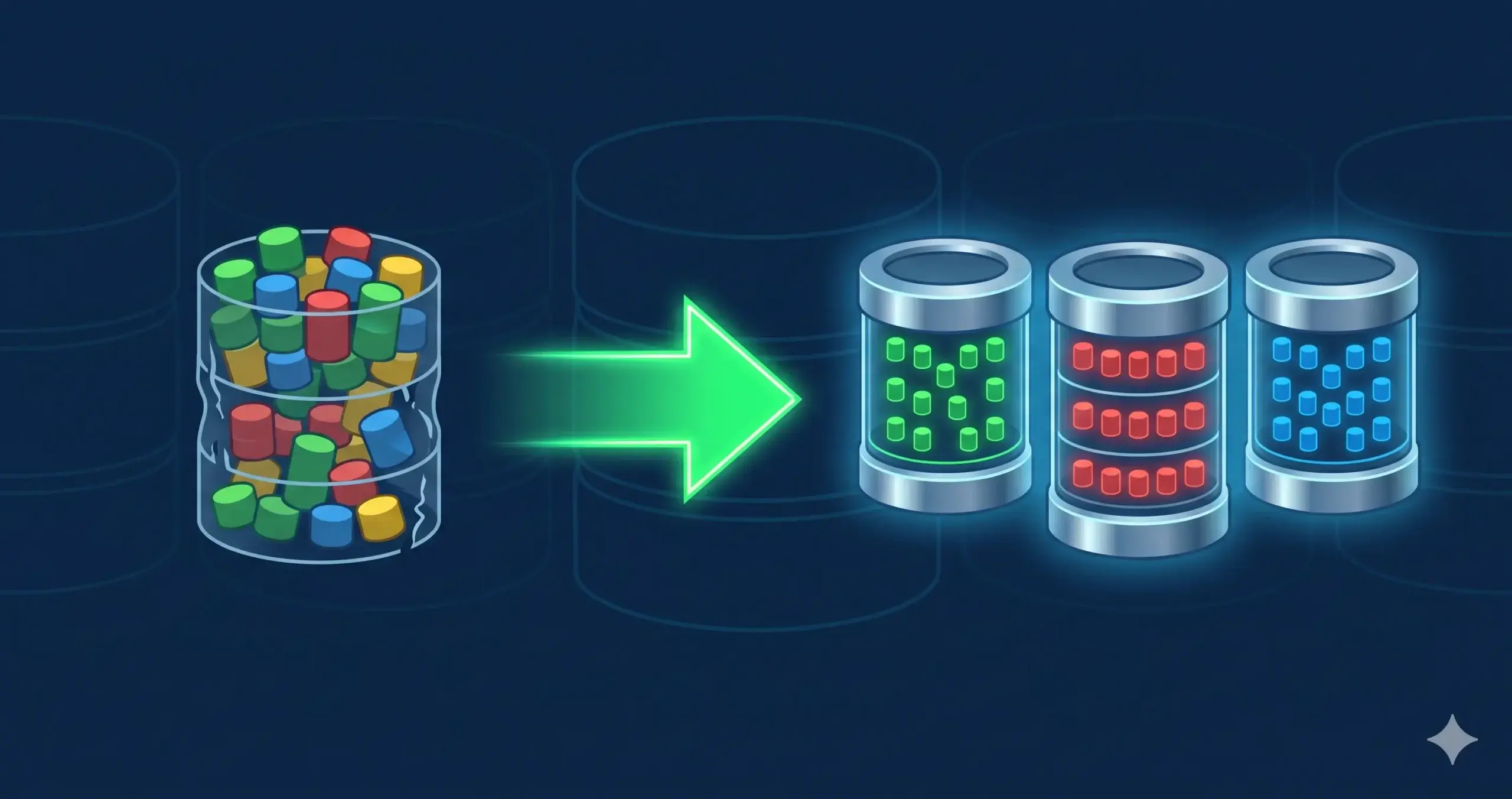
To rescue your enterprise deal, you do not need to burn your software to the ground. However, you must implement strict data isolation strategies. When scaling cloud infrastructure for enterprise clients, you have three distinct architectural paths to secure your multi-tenant SaaS database.
1. Row-Level Security (RLS)
If you must keep a shared database architecture, you must move the security logic out of your application code and into the database engine itself.
By implementing Row-Level Security (RLS) in PostgreSQL or SQL Server, you set strict database policies that act as a firewall. Even if a buggy API tries to pull the wrong data, the database engine will reject the query. This satisfies many mid-market compliance checks without requiring a massive infrastructure overhaul.
2. Schema-per-Tenant (Logical Isolation)
For true enterprise readiness, you need to physically separate the data structures. The “Schema-per-Tenant” model keeps all clients on the same database server, but gives every single client their own private schema (a dedicated set of tables).
This is the sweet spot for growing B2B companies. It prevents cross-tenant data bleeds entirely, makes backing up a single client’s data incredibly easy, and satisfies strict SOC2 isolation requirements.
3. Database-per-Tenant (Physical Sharding)
When you are closing massive, highly regulated clients (like banks or government agencies), they will demand physical isolation.
This requires a Database-per-Tenant architecture, often referred to as sharding. In this model, the enterprise client gets their own completely isolated database instance. While this is heavier to manage and requires elite custom web application development to route traffic dynamically, it provides the ultimate security guarantee. It also allows you to place the client’s database in a specific geographic region to comply with strict GDPR data residency laws.
Conclusion: Security is a Revenue Driver
Refactoring a multi-tenant SaaS database is an intense, highly technical process. But you must stop viewing security and compliance as an IT expense.
When you can confidently hand an enterprise CISO a clean SOC2 report and explain your sharded database architecture, you transition from a “risky startup” to a “trusted enterprise vendor.” Refactoring your database is the ultimate revenue unlock that allows you to close six-figure deals with confidence.
Is your MVP database preventing you from closing enterprise contracts?
👉 Book an Enterprise Security Code-Review Session We’ll audit your database architecture and map out a zero-downtime migration plan to isolate your tenant data.